Elliptic Links $286 Million Drift Protocol Exploit to North Korean State-Sponsored Hackers
Blockchain analysis firm Elliptic has identified North Korean traits in the $286 million Drift Protocol hack, citing sophisticated cross-chain laundering.
Blockchain analytics firm Elliptic has identified multiple indicators linking the $286 million exploit of Drift Protocol to the Democratic People’s Republic of Korea (DPRK).
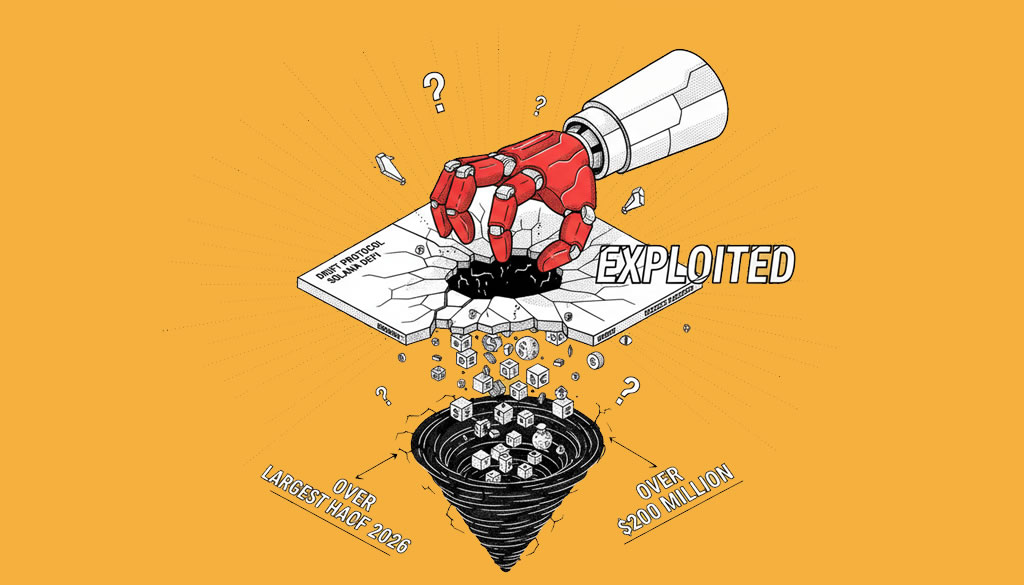
Blockchain intelligence firm Elliptic has released a report attributing the recent $286 million security breach of Drift Protocol to state-sponsored hackers from North Korea. The exploit, which took place on April 1, 2026, resulted in the drainage of nearly 50% of the protocol’s total value locked (TVL), marking it as the largest DeFi hack of the year to date.According to Elliptic, the on-chain behavior and laundering methodologies are consistent with the tradecraft of the Lazarus Group. The attackers reportedly spent over a week preparing the operation, utilizing durable nonce accounts and pre-signed transactions to bypass traditional security hurdles. By gaining unauthorized administrative control through sophisticated social engineering, the hackers were able to remove withdrawal limits and manipulate the protocol’s Security Council multisig threshold.The cross-chain laundering process began immediately after the funds were drained from Drift’s vaults. The attacker used Solana-based DEX aggregators to convert a variety of assets—including JLP, SOL, and wrapped Bitcoin—into USDC. These funds were subsequently bridged to the Ethereum blockchain and converted into ETH, a tactic frequently used by North Korean actors to obfuscate the trail of stolen crypto-assets before moving them into mixers like Tornado Cash.”The incident involved premeditated, meticulously planned on-chain activities and organized cross-chain laundering processes, resembling previous cryptocurrency thefts linked to North Korea,” Elliptic noted in its analysis. If the attribution is finalized, this would mark the 18th DPRK-linked criminal act tracked by the firm in 2026 alone.Drift Protocol confirmed that the attack did not stem from a smart contract vulnerability or a leak of seed phrases. Instead, the hackers exploited administrative hierarchies. The team is currently working with law enforcement and global exchanges to freeze the stolen assets and has suspended all protocol deposits and withdrawals until further notice.The exploit has had a significant impact on the Solana DeFi ecosystem, with Drift’s TVL plummeting from approximately $550 million to under $250 million within hours of the breach.
Disclaimer: This article is for informational purposes only and does not constitute advice of any kind. Readers should conduct their own research before making any decisions.
© Cryptopress. For informational purposes only, not offered as advice of any kind.
Latest Content
Lo Último
- Linux Foundation Launches x402 Foundation to Govern Coinbase’s Open AI Payments Protocol
- X to Auto-Lock Accounts Posting About Crypto for the First Time to Combat Scams
- Elliptic Links $286 Million Drift Protocol Exploit to North Korean State-Sponsored Hackers
- Coinbase CLO Signals Lawmakers Are ‘Very Close’ to Resolving Stablecoin Yield Dispute
- Drift Protocol Exploited for Over $200 Million in Largest Solana DeFi Hack of 2026
Related
- Drift Protocol Exploited for Over $200 Million in Largest Solana DeFi Hack of 2026 Solana-based perpetuals DEX Drift Protocol confirmed an active exploit on April 1, 2026, with on-chain data showing $200 million to $285 million drained. The team paused deposits and withdrawals, calling the incident 'not an April Fools joke' as the DRIFT...
- The biggest hack in DeFi history This week, hackers stole about $600 million worth of cryptocurrency from a Decentralized Finances (DeFi) network that specialized in enabling users to move digital assets linked to one blockchain to another. PolyNetwork, a multi-chain interoperability technology, is at the heart...
- Solana Airdrop Season: Your Comprehensive Guide to Capitalizing on Airdrops in the Solana Ecosystem Everything You Need to Know About the Solana Airdrop Season....
- Cryptocurrency Exchange WazirX Hacked for $230M, North Korea Suspected The attack targeted a multisig wallet, leading to the unauthorized transfer of funds....